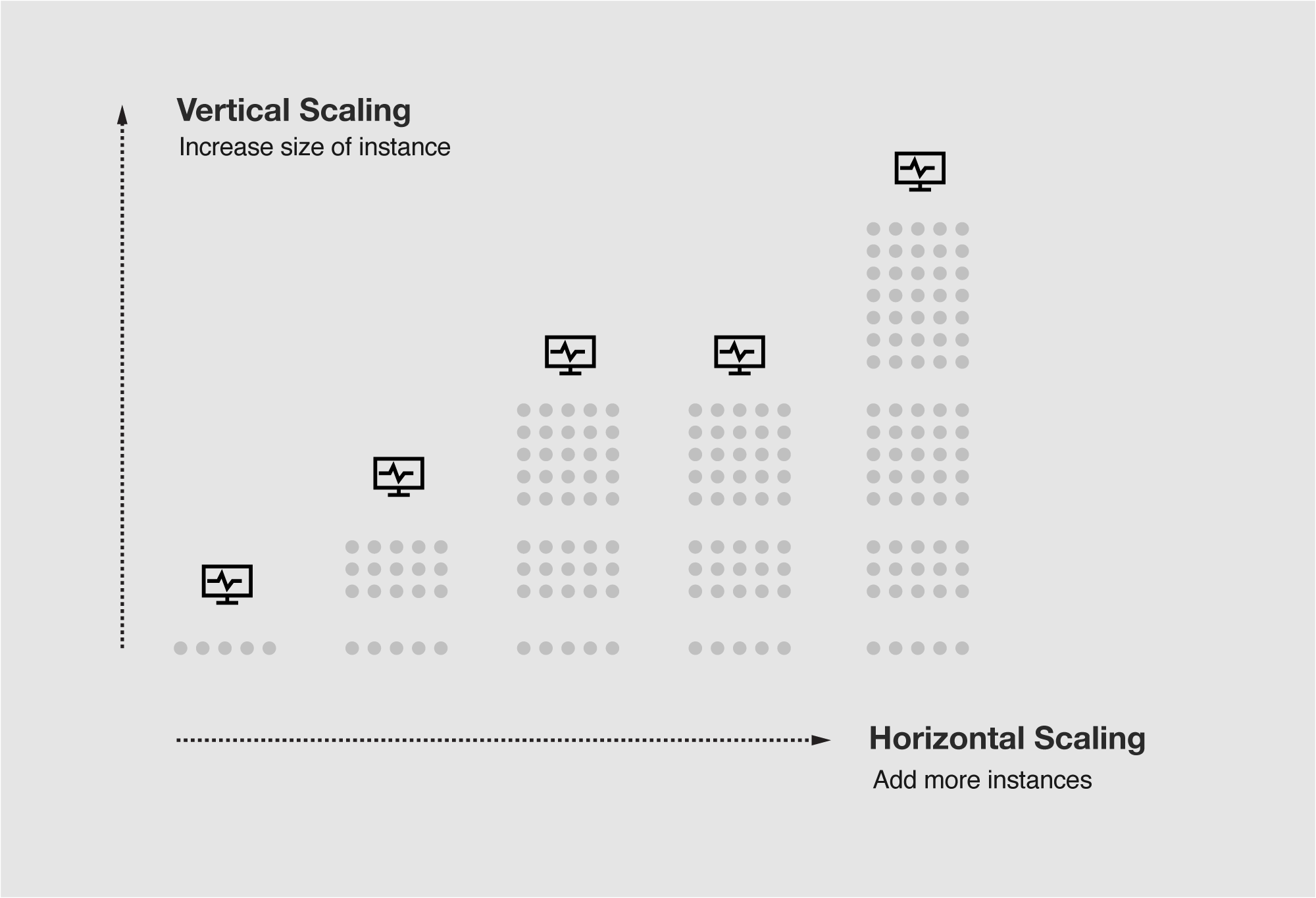
Auto-Scaling
Optimize productivity and cost with dynamic resource scaling. Configure the system to automatically maintain performance during demand spikes and scale down during lulls.
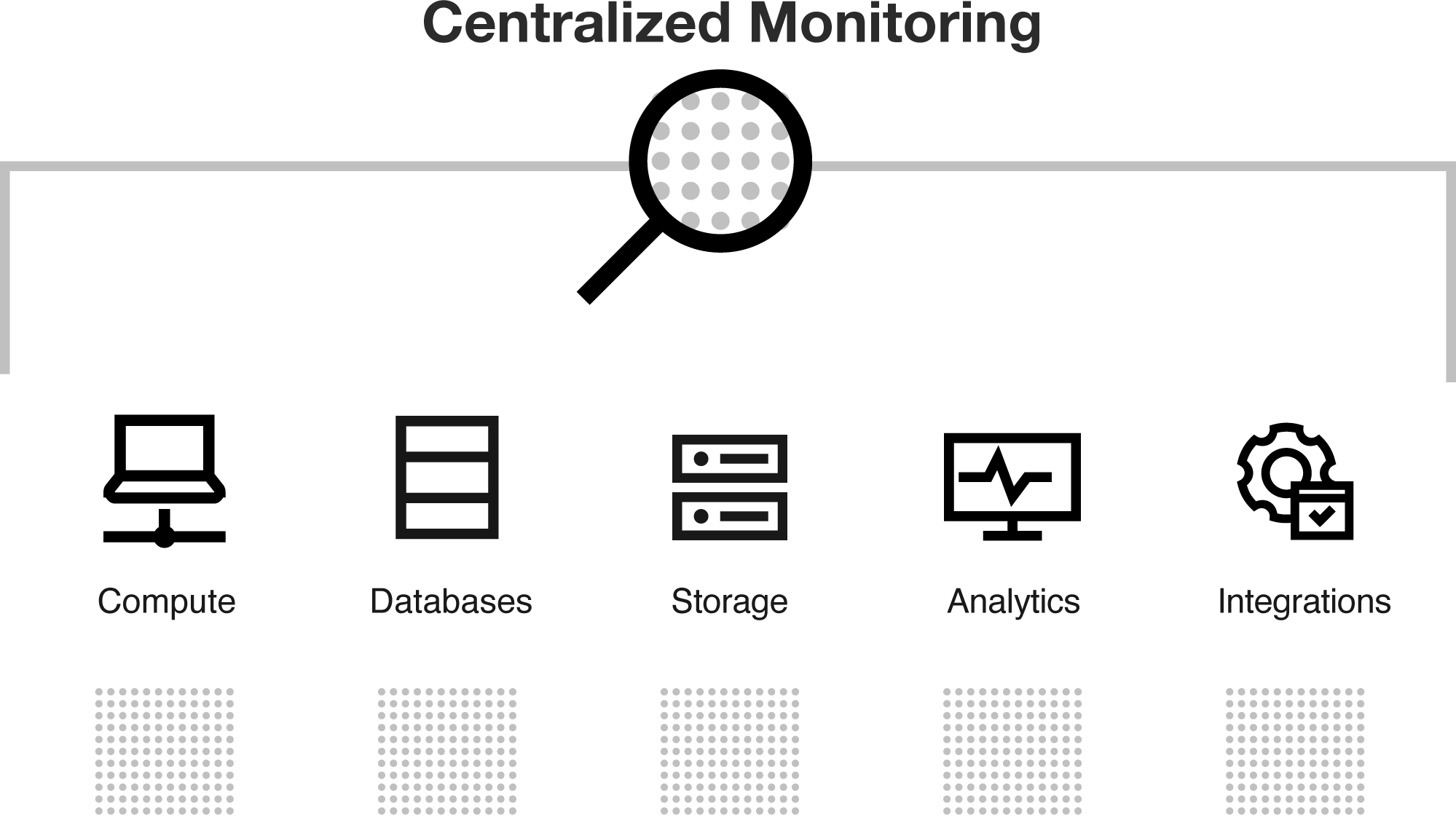
Monitoring
Maintain and balance the availability with cost of compute resources using end-to-end workload monitoring.
Through a central environment operations portal, administrators can monitor the state of analytic jobs and API performance, visualize current and historical environments, and configure autoscaling rules.
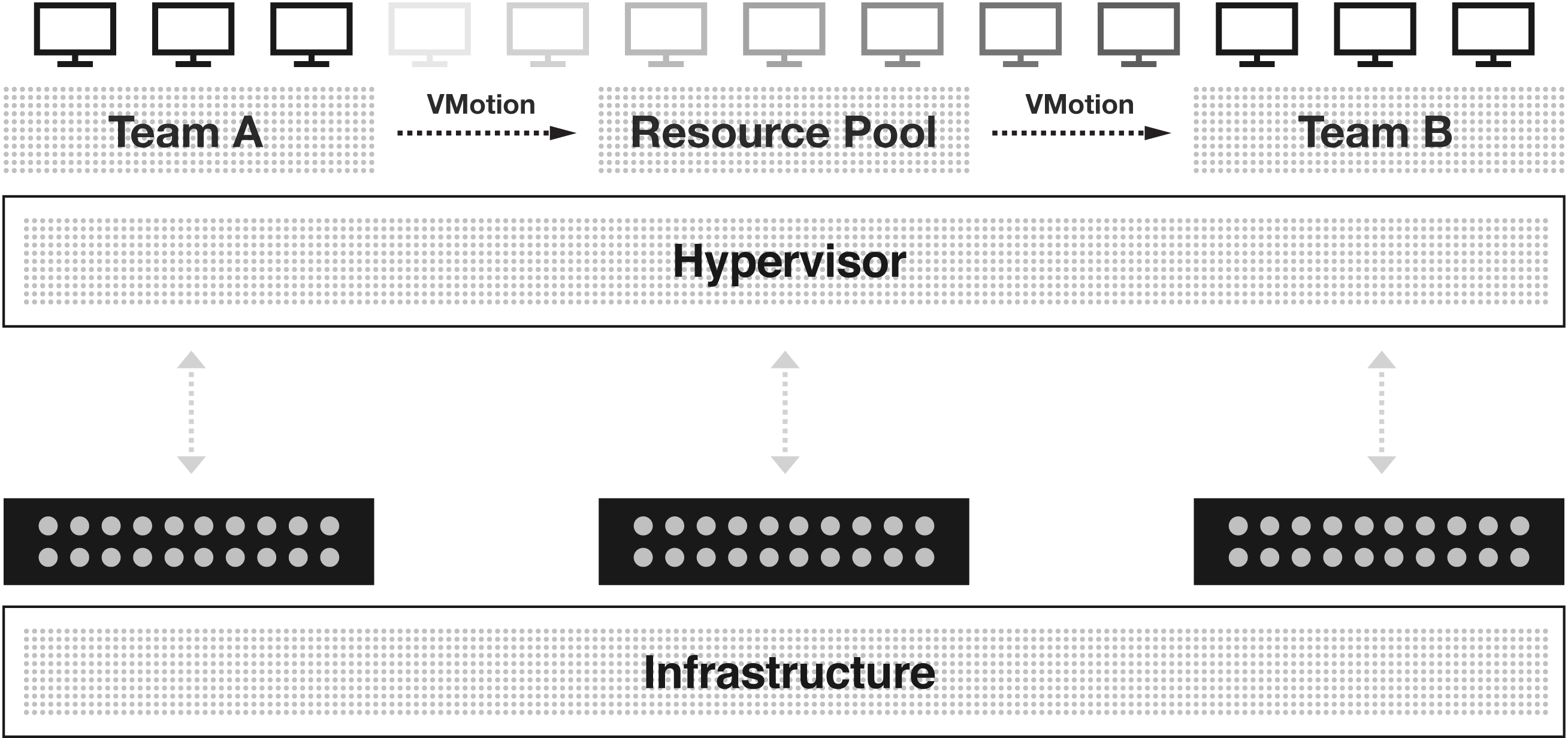
Workload Management
Meet business needs, boost productivity, and ensure performance with flexible workload configuration across all environments. Support mixed workloads in a single cluster and define hardware requirements for jobs.
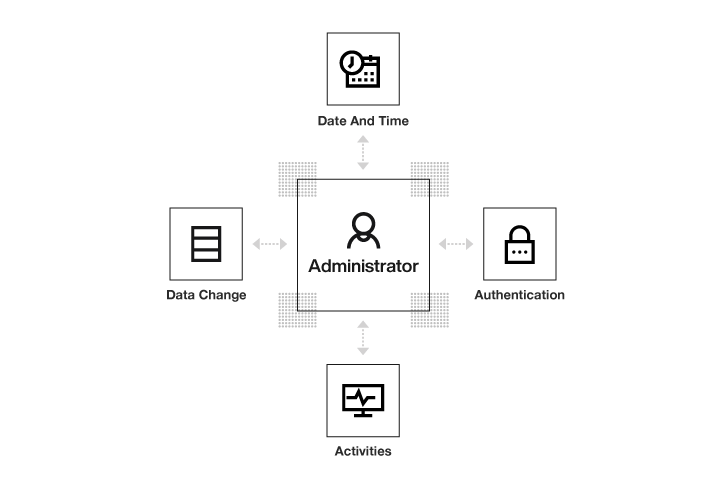
Automated Logging
Ensure traceability and maintain security through the automated logging of all access and data activities. Administrators can review all successful and unsuccessful authentication activities along with identity, action, and date and time of access, and every data change.
Take the Next Steps
Learn how our industry-leading Enterprise AI software products can help your organization.
Contact us at IR@C3.ai to learn more about investing at C3 AI.
For all other questions, please contact us here.


